Authors:
i) Ioan CONSTANTIN, Cyber Security Expert, Orange Romania,
ii) Cristian PAȚACHIA, Development & Innovation Manager, Orange Romania
The ever-expanding web of telecommunications infrastructure underpins the smooth functioning of modern society. From facilitating emergency response to enabling financial transactions and remote work, reliable communication networks are the lifeblood of our digital world. However, safeguarding this critical infrastructure presents a complex and constantly evolving challenge.
Orange Romania (ORO) is the largest telecommunications provider in Romania, and connects every other Romanian to state-of-the-art convergent, fixed, and mobile networks. We currently operate a vast 5G mobile network, covering major cities and offering fast, secure, and reliable connectivity. ORO's fixed networks are expanding to major geographies of Romania, and target multi-gigabit, fiber-to-the-building deployments. Our B2B services infrastructure is a key asset for the provision of end-to-end "telco-tech" services such as (managed) cyber security services, cloud services, co-location services, private fixed and mobile networks, as well as Edge-Cloud-IoT secure continuums.
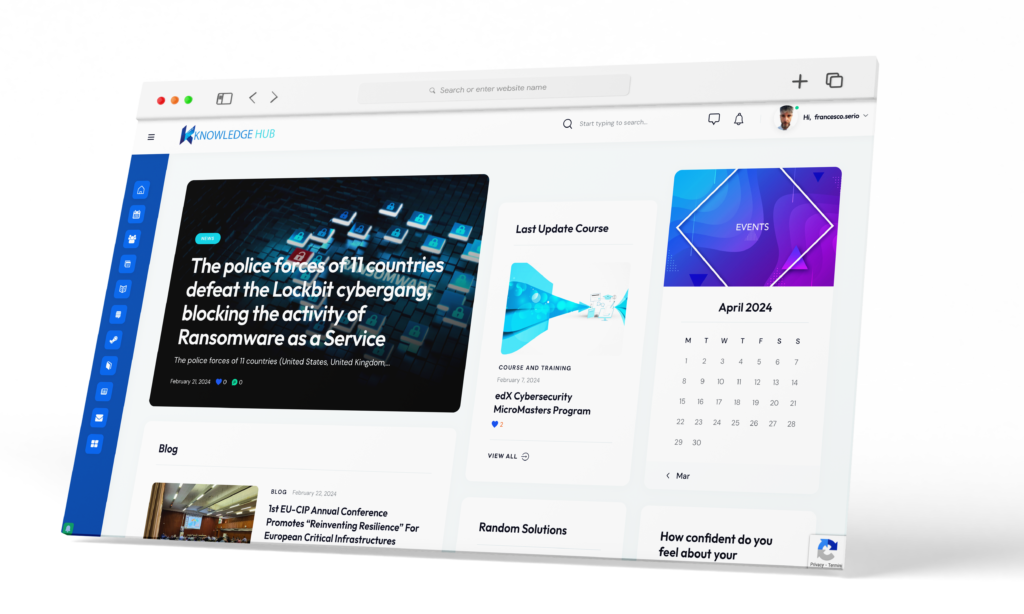
Furthermore, ORO is an active participant in key research, development, and innovation actions under the Horizon Europe framework, on the topics of Networks of the Future, Beyond-5G Connectivity, Cyber Security, Resilience Enhancement, and Critical Infrastructure Protection. One such project is EU-CIP, a first European Knowledge Hub and Policy Testbed for Critical Infrastructure Protection
This blog post delves into the key hurdles we face in protecting telecommunications infrastructure, and with the intricacies of supporting innovation in the field of CIP through participation in EU-CIP
1. The Evolving Threat Landscape:
Gone are the days of worrying solely about physical sabotage. Today, cyber threats pose a significant and growing risk. Malicious actors, ranging from state-sponsored hackers to criminal organizations, target vulnerabilities in telecommunications systems to disrupt services, steal data, or even sow chaos. The increasing sophistication of cyberattacks, coupled with the interconnected nature of these networks, makes them particularly susceptible. By maintaining an up-to-date, and relevant vernacular for complex, hybrid threats, Telcos can leverage knowledge sharing to pro-actively monitor and prevent complex threats. EU-CIP's Knowledge Hub works by consolidation of topical, vertical-relevant information that can be fed through the monitoring, detection and mitigation pipelines of Telecommunication operators and Telco Service Providers, to support end-to-end threat management functions.
2. Balancing Security and Innovation:
The telecommunications industry is constantly innovating, adopting new technologies like 5G and the Internet of Things (IoT). While these advancements bring undeniable benefits, they also introduce new security concerns. Legacy systems might not be equipped to handle the increased complexity and potential vulnerabilities associated with these technologies. Striking a balance between robust security measures and fostering innovation is crucial.
3. The Public-Private Divide:
Critical telecommunications infrastructure is often a complex ecosystem involving private companies and government agencies. This fragmented landscape can create challenges in establishing clear lines of responsibility for security. Differing priorities and information sharing limitations between public and private entities can hinder a coordinated response to threats. Lack of clarity in existing regulations, standards, and best-practices, means fragmentation at policy level for responsibilities in CIP, and will hinder visibility across supply chains, in complex environments. EU-CIP's addresses this gap by offering policy-testbed capabilities through which government entities, and private companies among CI verticals can test, evaluate, and validate public-facing policies.
4. The Human Factor:
Even the most sophisticated security systems can be compromised by human error or insider threats. Social engineering tactics can be used to trick employees into giving away sensitive information or compromising systems. Additionally, a lack of awareness or proper training among personnel can leave networks vulnerable.
5. The Cost of Security:
Implementing and maintaining robust security measures comes at a cost. Telecommunications companies need to balance the need for robust security with the financial realities of running a business. Finding the right balance between affordability and effectiveness is an ongoing challenge.
Navigating the Fortified Future
Despite these challenges, several potential solutions can bolster the resilience of our critical telecommunications infrastructure:
- Collaboration and Information Sharing: Fostering closer cooperation and secure information sharing between governments, security agencies, and telecom operators is essential. This allows for a more unified approach to threat identification, mitigation, and response.
- Standardization and Regulations: Establishing clear and enforceable security standards and regulations across the industry can help ensure a baseline level of protection. This fosters consistency and facilitates communication between stakeholders.
- Investing in Cybersecurity Workforce Development: Building a skilled cybersecurity workforce equipped to address evolving threats is paramount. This includes fostering awareness among telecommunications personnel and upskilling existing professionals.
- Adopting a Security-by-Design Approach: Integrating security considerations into the design and development of new telecommunications technologies is crucial. This proactive approach can help minimize vulnerabilities from the outset.
Conclusion
Protecting critical telecommunications infrastructure is a continuous endeavour. By acknowledging the challenges and working towards collaborative solutions, we can ensure the continued reliability and security of this vital lifeline in our increasingly digital world.